Protecting Your E-commerce Business: Understanding Zero-Day Vulnerabilities in Website Builders
Zero-day vulnerability website threats don’t wait for business hours. Every minute your e-commerce site stays unmonitored is a chance for hackers to slip in unnoticed. With sensitive payment data at stake, relying on basic security won’t cut it—you need website security monitoring that runs 24/7. Here’s why managed IT services Indianapolis providers prioritize nonstop protection to keep your store safe around the clock.
The Growing Threat of Zero-Day Vulnerabilities in E-commerce Platforms
Zero-day vulnerabilities represent one of the most serious threats facing online businesses today. These security flaws exist in software before developers become aware of them, leaving no time for patches or fixes. For e-commerce store owners, a zero-day vulnerability website attack can mean compromised customer data, stolen payment information, and irreparable damage to your brand reputation.
Website builders like WordPress, Shopify, Magento, and WooCommerce power millions of online stores worldwide. While these platforms offer convenience and functionality, they also present attractive targets for cybercriminals. When a zero-day exploit emerges in popular website builders, hackers race to exploit as many sites as possible before security teams can respond.
The financial impact of these breaches extends far beyond immediate losses. E-commerce businesses face regulatory fines under PCI DSS compliance requirements, potential lawsuits from affected customers, and the long-term cost of rebuilding customer trust. Your store processes sensitive payment data every single day, making you a prime target for sophisticated attacks that exploit unknown vulnerabilities.
Why Traditional Security Measures Fall Short
Many e-commerce store owners rely on standard security plugins, SSL certificates, and periodic security scans. While these tools provide baseline protection, they cannot defend against zero-day threats. By definition, zero-day vulnerabilities are unknown to security software until after attackers have already begun exploiting them.
Traditional security approaches operate on a reactive model. They wait for threats to be identified, analyzed, and added to threat databases before they can provide protection. This gap between vulnerability discovery and patch deployment creates a window of opportunity that skilled hackers exploit with devastating efficiency.
Your e-commerce platform requires a different approach. Protecting websites from hackers in today’s threat environment demands continuous monitoring, behavioral analysis, and immediate response capabilities. When a zero-day vulnerability website attack occurs, every second counts. Automated tools alone cannot provide the nuanced judgment required to distinguish between legitimate customer activity and malicious intrusion attempts.
The Critical Role of 24/7 Website Security Monitoring
Round-the-clock website security monitoring serves as your first line of defense against zero-day exploits. Professional monitoring teams watch for suspicious patterns, unusual traffic spikes, and anomalous behavior that might indicate an attempted breach. This constant vigilance ensures that threats are identified and addressed before they can compromise your customer data.
Real-time monitoring systems track multiple security indicators simultaneously. They analyze login attempts, file modifications, database queries, and network traffic patterns. When monitoring systems detect activities that deviate from established baselines, security professionals can investigate immediately, regardless of whether the threat matches known attack signatures.
For e-commerce businesses, the value of continuous monitoring becomes clear when you consider the timing of cyberattacks. Hackers frequently launch attacks during off-hours, weekends, and holidays when they assume security teams are unavailable. A zero-day vulnerability website exploit discovered on a Friday evening could compromise thousands of customer records before Monday morning if no one is watching.
Managed IT services Indianapolis providers understand that e-commerce operations never sleep. Your customers shop at all hours, which means your security posture must remain equally vigilant. Professional monitoring teams work in shifts to ensure that trained security experts are always available to respond to emerging threats.
How Managed IT Services Provide Comprehensive Protection
Partnering with managed IT services Indianapolis specialists gives your e-commerce business access to enterprise-level security resources without the overhead of maintaining an in-house security operations center. These partnerships deliver multiple layers of protection specifically designed to address zero-day threats.
Managed service providers deploy advanced intrusion detection systems that monitor your website infrastructure continuously. These systems employ machine learning algorithms to establish normal behavior patterns for your site. When activities deviate from these patterns, the system generates alerts for human security analysts to review.
Professional security teams maintain current knowledge of emerging threats across the cybersecurity industry. They participate in information-sharing networks that provide early warnings about newly discovered vulnerabilities. This intelligence allows them to implement protective measures for your site even before official patches become available.
Website security monitoring through managed services includes regular vulnerability assessments, penetration testing, and security audits. These proactive measures identify potential weaknesses in your e-commerce platform before attackers can exploit them. Security professionals examine your site architecture, third-party integrations, custom code, and server configurations to ensure comprehensive protection.
Understanding the Anatomy of a Zero-Day Attack
Zero-day attacks typically unfold in predictable stages, and understanding this progression helps explain why immediate detection matters so much. Attackers begin with reconnaissance, scanning websites to identify the specific platform version and installed plugins. They compare this information against their knowledge of unpatched vulnerabilities.
Once attackers identify a vulnerable target, they attempt to exploit the weakness to gain unauthorized access. This might involve injecting malicious code, manipulating database queries, or bypassing authentication mechanisms. The initial breach often occurs through a small entry point that grants limited access.
After establishing a foothold, attackers work to escalate their privileges and expand their access throughout your system. They may install backdoors to ensure continued access even if the original vulnerability gets patched. This lateral movement through your infrastructure can happen within minutes if undetected.
The final stage involves data exfiltration, where attackers extract customer payment information, personal data, and business records. Sophisticated criminals take care to avoid triggering obvious alarms during this process. They may extract data gradually over time or disguise their activities to blend with legitimate traffic patterns.
Protecting websites from hackers requires interrupting this attack chain as early as possible. Website security monitoring systems are designed to detect suspicious activities at each stage, providing multiple opportunities to stop the attack before data is compromised.
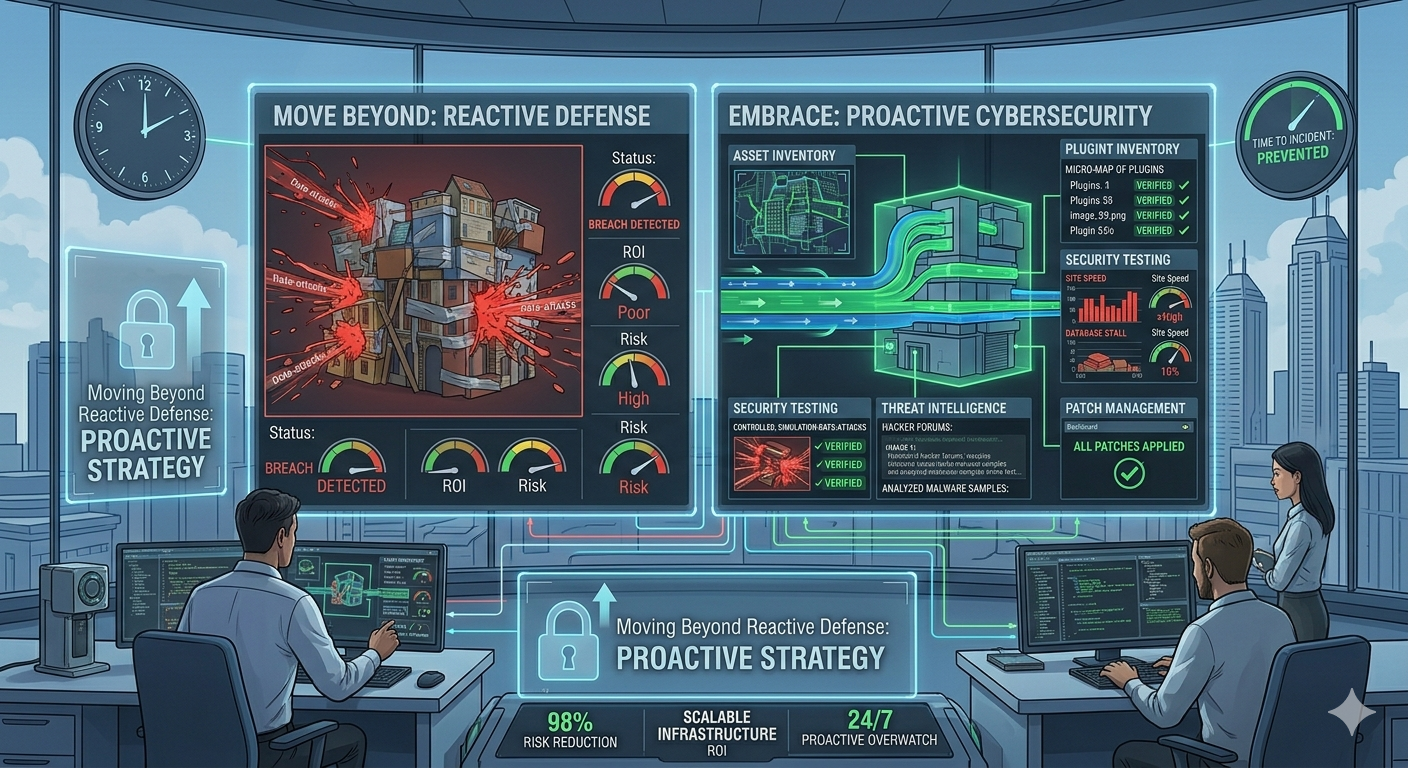
Proactive Cybersecurity: Moving Beyond Reactive Defense
Proactive cybersecurity represents a fundamental shift in how businesses approach digital security. Rather than waiting for attacks to occur and then responding, proactive strategies anticipate threats and implement defenses before vulnerabilities can be exploited.
This approach begins with comprehensive asset inventory. You cannot protect what you don’t know you have. Managed IT services Indianapolis teams catalog every component of your e-commerce infrastructure, including third-party plugins, custom modifications, and integration points. This complete visibility ensures nothing falls through the security cracks.
Regular security testing forms another pillar of proactive cybersecurity. Penetration testers simulate real-world attack scenarios against your e-commerce platform, identifying weaknesses before criminals can find them. These controlled tests reveal how attackers might chain together multiple minor vulnerabilities to achieve major breaches.
Threat intelligence gathering keeps your security posture aligned with current attack trends. Security professionals monitor hacker forums, analyze malware samples, and track emerging exploit techniques. This intelligence informs defensive strategies tailored to the specific threats facing e-commerce businesses.
Patch management processes ensure that known vulnerabilities get addressed promptly. While zero-day vulnerabilities by definition have no available patches, most successful attacks actually exploit older, well-known vulnerabilities that organizations failed to patch. Maintaining current software versions eliminates many attack vectors.
The Business Case for Professional Security Monitoring
Investing in professional website security monitoring delivers measurable returns that extend beyond breach prevention. E-commerce businesses that demonstrate strong security practices build customer confidence, which translates directly into increased sales and customer retention.
Compliance requirements for businesses handling payment card data mandate specific security controls. PCI DSS standards require regular security monitoring, vulnerability scanning, and incident response capabilities. Professional managed services ensure your business meets these obligations while documenting compliance for auditors.
The cost of a data breach extends far beyond immediate financial losses. Research shows that businesses suffer long-term revenue declines following security incidents as customers lose trust and take their business elsewhere. The reputational damage from a single breach can take years to overcome.
Insurance companies increasingly require proof of professional security monitoring as a condition for cyber liability coverage. Policies may exclude coverage for breaches that occur when basic security practices were not followed. Partnering with managed IT services Indianapolis providers demonstrates due diligence that can affect both coverage availability and premium costs.
Time savings represent another significant benefit. Your IT team can focus on business growth initiatives rather than constant security fire drills. Professional monitoring services handle the routine security tasks while escalating only genuine threats that require your attention.
Selecting the Right Managed IT Security Partner
Choosing a managed IT services provider requires careful evaluation of their capabilities, experience, and approach to e-commerce security. Not all providers offer the same level of expertise in protecting websites from hackers, particularly in the specialized context of online retail.
Look for providers with specific experience securing e-commerce platforms. They should understand the unique requirements of online stores, including payment processing security, customer data protection, and the performance implications of security controls. Generic IT support cannot address the specialized needs of businesses handling financial transactions.
Response time commitments matter enormously when dealing with zero-day vulnerability website threats. Clarify what “24/7 monitoring” actually means. Some providers offer automated monitoring with business-hours response, while others maintain staffed security operations centers around the clock. For e-commerce businesses, human expertise available immediately provides superior protection.
Evaluate the provider’s threat intelligence capabilities. Strong security partners participate in industry information-sharing programs, maintain relationships with security researchers, and actively track emerging threats. This intelligence network provides early warning of new vulnerabilities affecting your platform.
Communication practices during security incidents can make or break your response effectiveness. Your provider should have clear escalation procedures, defined contact protocols, and established processes for coordinating response activities. Ask for examples of how they have handled previous security incidents for e-commerce clients.
Implementing Layered Security for E-commerce Sites
Comprehensive protection against zero-day exploits requires multiple overlapping security layers. This defense-in-depth approach ensures that if one security control fails, others remain in place to prevent or limit damage.
Perimeter security forms the outermost layer, filtering malicious traffic before it reaches your website. Web application firewalls analyze incoming requests, blocking those that exhibit attack patterns. While these firewalls cannot stop unknown zero-day exploits by signature, they can prevent many attack techniques through behavioral analysis.
Application-level security focuses on the website platform itself. This includes keeping your e-commerce software current, removing unnecessary plugins, and hardening configurations according to security best practices. Regular code reviews identify vulnerabilities in custom functionality before they can be exploited.
Database security protects the sensitive customer information stored in your systems. Encryption, access controls, and query monitoring prevent unauthorized data access. Even if attackers compromise your website, proper database security can prevent them from extracting customer payment information.
Network segmentation isolates different components of your infrastructure. Your payment processing systems should operate in separate network zones from your public-facing website. This compartmentalization limits how far attackers can move through your systems after an initial breach.
Backup and recovery systems provide a final safety net. Regular automated backups stored in secure off-site locations ensure you can restore operations quickly if an attack succeeds. Test your recovery procedures regularly to verify that backups are functional and complete.
The Future of E-commerce Security
The threat environment facing e-commerce businesses continues to grow more sophisticated. Attackers employ automation, artificial intelligence, and coordinated campaigns that can identify and exploit vulnerabilities across thousands of sites simultaneously. Defending against these evolving threats requires equally advanced protective measures.
Artificial intelligence and machine learning will play increasing roles in both attack and defense. Security monitoring systems already use these technologies to identify anomalous behavior patterns that might indicate zero-day exploits. Future developments will enable even faster threat detection and automated response capabilities.
Regulatory requirements for data protection continue to expand globally. New privacy laws impose strict obligations on businesses that collect customer information. Security monitoring and incident response capabilities will become legal requirements, not just best practices.
The shift toward cloud-based e-commerce platforms introduces new security considerations. While major platforms invest heavily in security, the shared responsibility model means store owners must still protect their specific implementations. Understanding where platform security ends and your responsibility begins is critical for comprehensive protection.
Supply chain attacks targeting third-party plugins and integrations represent a growing threat vector. Attackers compromise trusted software components, which then spread malicious code to thousands of websites. Monitoring for suspicious behavior from supposedly trusted components becomes increasingly important.
Taking Action to Protect Your E-commerce Business
The question facing e-commerce store owners is not whether to invest in professional security monitoring, but how quickly you can implement it. Every day without comprehensive protection represents a calculated risk with your customer data and business reputation.
Begin by assessing your current security posture honestly. Document your existing security controls, monitoring capabilities, and incident response procedures. Identify gaps between your current state and the level of protection your business requires given the sensitivity of data you handle.
Research managed IT services Indianapolis providers with demonstrated expertise in e-commerce security. Request detailed information about their monitoring capabilities, response procedures, and experience with zero-day vulnerability website threats. Ask for references from other e-commerce clients who can speak to the provider’s effectiveness.
Develop a transition plan that implements professional monitoring without disrupting your business operations. Good managed service providers can often begin monitoring immediately while gradually implementing more comprehensive security improvements over time.
Establish clear communication channels and escalation procedures with your security partner. Ensure that key personnel in your organization know how to report suspicious activities and whom to contact during security incidents. Regular drills help verify that these procedures work when needed.
Commit to ongoing security awareness within your organization. Even the best technical controls cannot prevent breaches caused by human error. Regular training helps your team recognize phishing attempts, practice good password hygiene, and understand their role in protecting websites from hackers.
Building Long-Term Security Resilience
Protecting your e-commerce business from zero-day vulnerabilities requires more than implementing security tools. It demands a commitment to continuous improvement, ongoing vigilance, and partnership with security professionals who understand the unique challenges facing online retailers.
Website security monitoring provides the foundation for this protection. Round-the-clock surveillance by experienced security analysts ensures that threats are identified and addressed immediately, regardless of when they occur. This constant vigilance transforms security from a periodic concern into a continuous business function.
Managed IT services Indianapolis providers bring specialized expertise that most businesses cannot develop in-house. They maintain current knowledge of emerging threats, employ advanced security technologies, and provide the human judgment required to distinguish genuine threats from false alarms.
Proactive cybersecurity approaches shift your security posture from reactive to anticipatory. By identifying and addressing vulnerabilities before attackers exploit them, you reduce risk while avoiding the disruption and damage of actual security incidents.
Your customers trust you with their most sensitive information when they make purchases from your store. Honoring that trust requires implementing security measures commensurate with the responsibility you have accepted. Professional security monitoring demonstrates your commitment to protecting customer data.
The investment in comprehensive security monitoring pays dividends through reduced breach risk, maintained customer confidence, regulatory compliance, and peace of mind. You can focus on growing your business knowing that security professionals are watching over your digital assets continuously.
Zero-day vulnerability website threats will continue to emerge as long as software exists. The question is whether those threats will find your e-commerce site protected by professional monitoring and proactive defenses, or whether they will find an easy target. The choice you make today determines which scenario unfolds tomorrow.