As we navigate the digital commerce landscape of 2026, the intersection of marketing and information technology has never been more critical. While marketing teams invest heavily in driving qualified traffic to digital storefronts, a silent and highly sophisticated adversary is actively undermining these efforts: the modern malicious bot.
For years, bots were viewed primarily as a nuisance—automated scripts that scraped pricing data or spammed comment sections. However, the threat vector has evolved dramatically. Today, sophisticated, AI-driven botnets are executing targeted, high-speed attacks directly at the most vulnerable point of your sales funnel: the checkout page.
For e-commerce executives, IT directors, and marketing leaders, understanding and neutralizing these threats is no longer optional. It is a fundamental requirement for protecting revenue, preserving marketing return on investment (ROI), and maintaining customer trust.
Here is an executive overview of the 2026 bot threat landscape and the strategic measures required to defend your checkout page.
The Evolution of the Malicious Bot in 2026
The bots of the early 2020s relied on basic scripts and static IP addresses. They were easily thwarted by traditional Web Application Firewalls (WAFs) and standard CAPTCHA challenges. However, the proliferation of generative AI and machine learning has armed cybercriminals with unprecedented capabilities.
Today’s bots are designed specifically to mimic human behavior. They utilize vast networks of residential proxies, routing their traffic through legitimate household IP addresses to evade geographic blocking. They are programmed to simulate human mouse movements, keystroke dynamics, and browsing delays. Furthermore, modern bots employ advanced computer vision algorithms capable of solving traditional visual CAPTCHAs in milliseconds.
When these sophisticated networks target an e-commerce checkout page, traditional perimeter defenses are often entirely blind to the intrusion until the damage is already done.
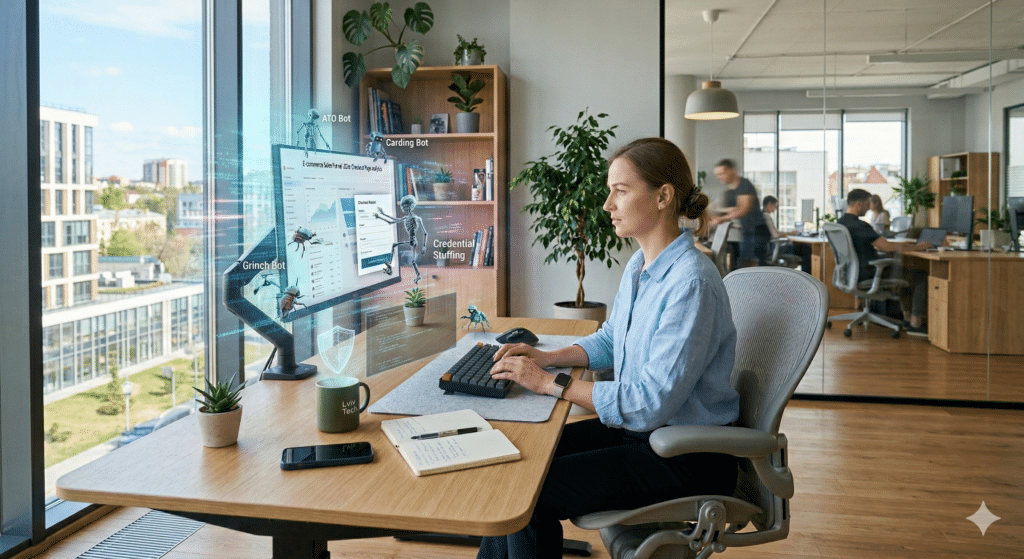
The Primary Threats to Your Checkout Page
When botnets reach your payment gateway, they typically execute one of three highly destructive attack methodologies.
1. Carding and Payment Fraud
Carding is the automated process of testing stolen credit card information. Cybercriminals purchase massive databases of compromised credit card numbers on the dark web. Because they do not know which cards are still active or what the correct CVV numbers are, they deploy bots to rapidly test these credentials on e-commerce checkout pages.
The bots initiate thousands of low-value transactions. If a transaction goes through, the bot immediately logs the card as “live,” allowing the criminal to use it for high-value purchases elsewhere or sell the verified data at a premium.
For the e-commerce merchant, the consequences are severe. Even if the fraudulent transactions are caught, the merchant is often hit with massive authorization fees from their payment processor for the thousands of failed attempts. If the transactions succeed and are later reported as fraud, the merchant faces chargeback fees, loss of inventory, and the risk of having their merchant account terminated entirely.
2. Inventory Hoarding and Scalping
Inventory hoarding bots—commonly known as “Grinch bots” or “scalper bots”—target high-demand, limited-edition products. The moment a highly anticipated product launches, these bots bypass virtual waiting rooms, automatically add the item to their carts, and complete the checkout process in fractions of a second.
In some variations, the bots do not even complete the purchase. Instead, they hold the items in their carts, locking up the inventory and making it unavailable to legitimate human customers. This artificial scarcity frustrates genuine buyers, damages the brand’s reputation, and forces consumers to buy the product at inflated prices on secondary markets.
3. Account Takeover (ATO) at Checkout
Many e-commerce sites encourage users to create accounts to save their shipping details and payment methods for a frictionless checkout experience. Bots exploit this by executing credential stuffing attacks—using lists of usernames and passwords stolen from other website breaches to attempt logins on your site.
Once the bot successfully accesses a user account, it proceeds to the checkout page. Since the payment information is already saved, the bot can effortlessly purchase goods or drain the user’s accumulated loyalty points, routing the stolen assets to alternative addresses.
The Hidden Marketing Cost of Bot Attacks
While IT and security teams view bot attacks as a cybersecurity incident, marketing departments often bear the invisible costs. The presence of sophisticated bots on your checkout page actively destroys marketing data and drains advertising budgets.
- Skewed Analytics: Bots inflate traffic metrics and artificially spike cart abandonment rates. When marketing teams analyze this corrupted data, they may incorrectly conclude that a specific ad campaign is failing or that the checkout UI is poorly designed, leading to misguided strategic pivots.
- Wasted Retargeting Budgets: When bots abandon carts, automated marketing systems trigger retargeting campaigns. Your company ends up spending premium advertising dollars serving ads and sending promotional emails to automated scripts that will never make a purchase.
- Brand Reputation Damage: When human customers cannot purchase inventory due to scalper bots, or when their accounts are compromised via ATO, the brand’s trust equity is severely damaged. In the highly competitive landscape of 2026, a customer who feels unsafe or frustrated on your site will simply click away to a competitor.
Strategic Defense: Next-Generation Protection for Your Digital Storefront
Defending against 2026-era bots requires a paradigm shift. Static rules and reactive blocking are insufficient. E-commerce platforms must implement dynamic, multi-layered defenses that operate in real-time without adding friction for legitimate human buyers.
Implementing Behavioral Biometrics
Because modern bots use residential IPs and can solve CAPTCHAs, security systems must look beyond what the user is to how the user is behaving. Behavioral biometrics analyzes the subtle nuances of user interaction.
Does the user navigate straight to the checkout page with zero dwell time? Are the mouse movements mathematically perfect rather than organic and erratic? Is the typing speed impossibly fast? By analyzing these micro-behaviors in the background, advanced threat protection systems can flag and challenge anomalous activity before the checkout button is even clicked.
Advanced Device Fingerprinting
Device fingerprinting goes beyond checking IP addresses. It analyzes the specific configuration of the user’s device—evaluating browser versions, installed fonts, operating systems, hardware specifications, and battery APIs.
Bot operators often use headless browsers or virtual machines that possess distinct, identifiable digital fingerprints. By cross-referencing these fingerprints against global databases of known bot infrastructure, security systems can intercept malicious traffic regardless of the IP address being used.
API Security and Rate Limiting
Modern e-commerce sites rely heavily on Application Programming Interfaces (APIs) to process payments, check inventory, and authenticate users. Bots frequently bypass the visual website entirely, targeting these APIs directly to execute attacks at maximum speed.
Robust API security is paramount. This includes implementing strict rate limiting (restricting the number of requests a single entity can make within a specific timeframe), requiring rigorous authentication protocols for API access, and continuously monitoring API traffic for anomalous spikes indicative of a carding or scraping attack.
The Elevated-Marketing Solution: Integrating IT and Marketing
The most significant vulnerability in many modern businesses is the structural silo between the IT department and the Marketing department. Marketing prioritizes a frictionless, high-speed user experience to maximize conversions, while IT prioritizes strict security protocols that often inadvertently block legitimate buyers.
At Elevated-Marketing.io, we recognize that true e-commerce success requires a unified approach. Threat protection cannot exist in a vacuum; it must be carefully calibrated to protect the perimeter without cannibalizing the conversion rate.
By integrating our cybersecurity expertise with our deep understanding of digital marketing and conversion rate optimization (CRO), we design e-commerce environments that are resilient against advanced botnets while remaining perfectly streamlined for your actual customers. We ensure your analytics remain pure, your ad spend is directed exclusively at humans, and your checkout page remains a secure engine for revenue generation.
Do not wait until a carding attack decimates your merchant account or scalper bots ruin your next product launch. Secure your digital future today. Contact the team at Elevated-Marketing.io for a comprehensive audit of your current e-commerce threat protection infrastructure, and let us fortify your checkout page for 2026 and beyond.
